Penetration Testing
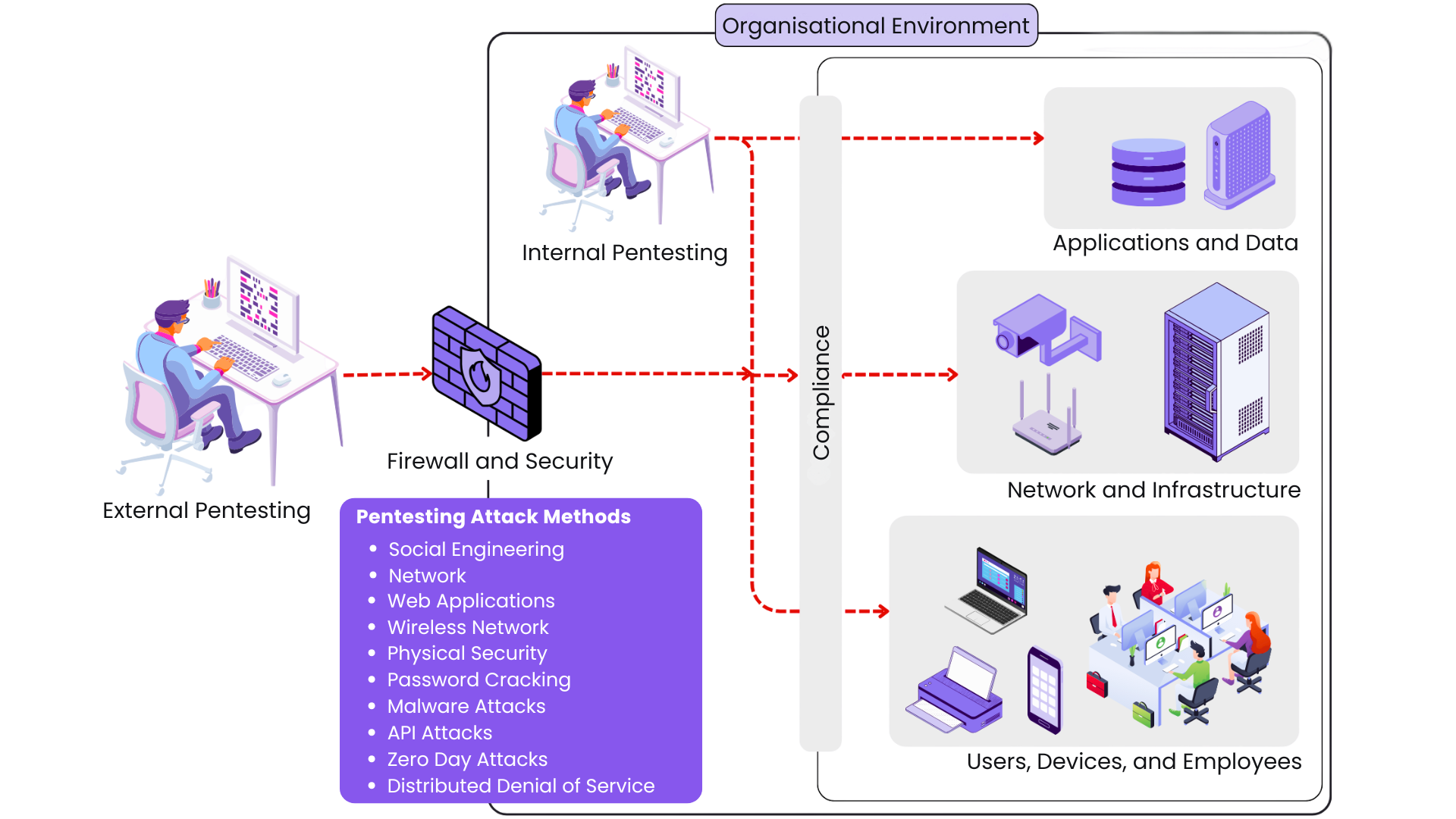
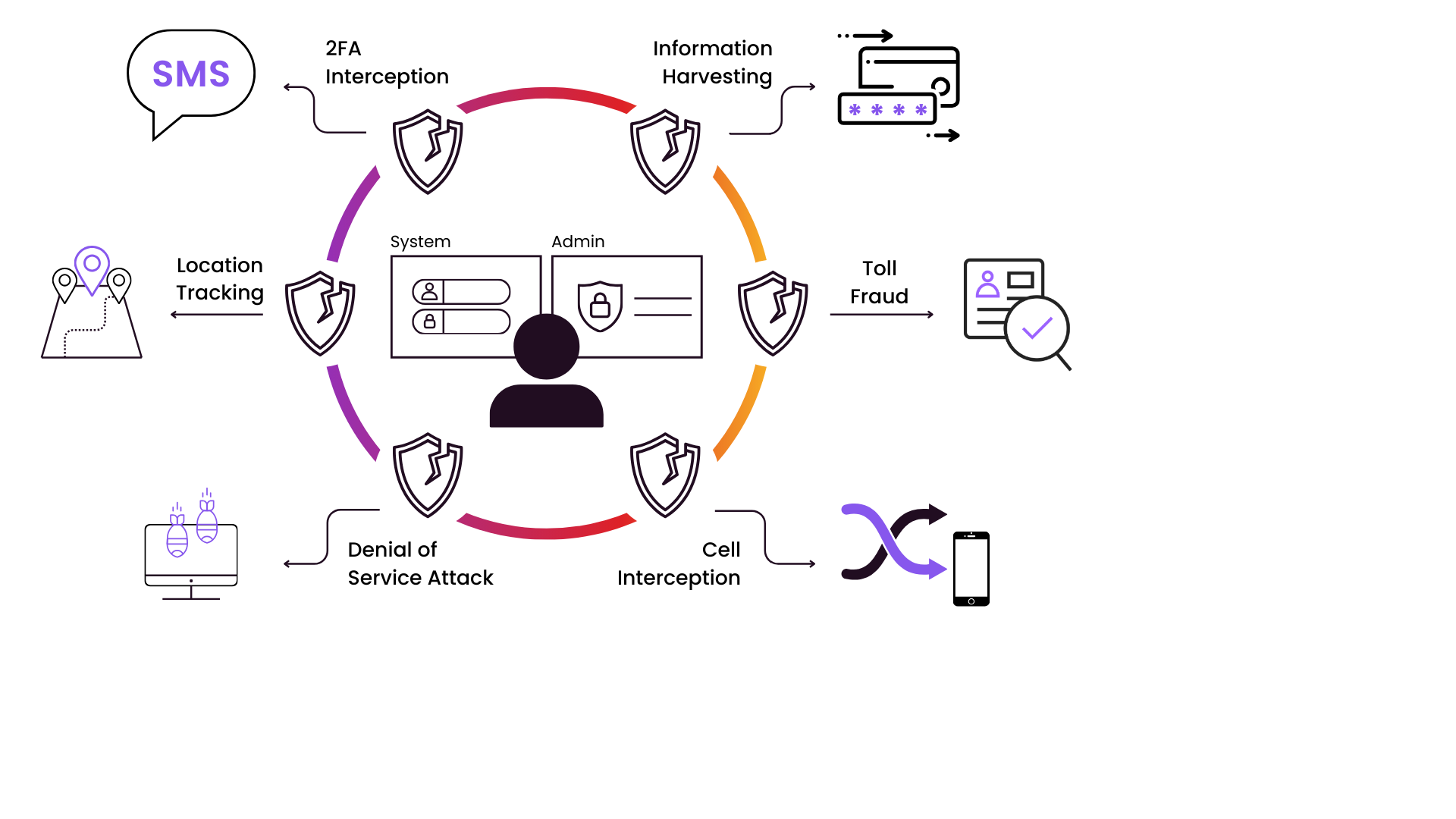
Penetration testing, often referred to as pen testing or ethical hacking, is a method used to evaluate the security of a computer system, network, or web application by simulating real-world cyberattacks. The primary goal is to identify vulnerabilities that could be exploited by malicious actors. Used effectively, it can be an essential component of a robust cybersecurity strategy, helping you proactively identify and address security gaps before they can be exploited by attackers. Some key aspects of pen testing include:
Vulnerability Identification
Use of a combination of automated tools and manual techniques to find security weaknesses

Exploitation
Once vulnerabilities are identified, exploiting them to understand the potential impact of an attack

Reporting
The findings are documented in a detailed report including vulnerabilities discovered, methods used to exploit them, and recommendations for remediation


Risk Assessment
Pen testing aids organisations to understand their security posture and prioritize fixes based on the severity of the vulnerabilities

Verify Fixes
Re-test to confirm vulnerability remediation and close security gaps, confirming a strengthened security posture

Ongoing Regular Testing
Automated tools can be used both on the external facing IP's address as well as internal address's. They complement regular scheduled manual pen-testing
Pen Testing
Pen Testing

Vulnerability Identification
Use of a combination of automated tools and manual techniques to find security weaknesses

Exploitation
Once vulnerabilities are identified, exploiting them to understand the potential impact of an attack

Reporting
The findings are documented in a detailed report including vulnerabilities discovered, methods used to exploit them, and recommendations for remediation

Risk Assessment
Pen testing aids organisations to understand their security posture and prioritize fixes based on the severity of the vulnerabilities

Verify Fixes
Re-test to confirm vulnerability remediation and close security gaps, confirming a strengthened security posture

Ongoing Regular Testing
Automated tools can be used both on the external facing IP's address as well as internal address's. They complement regular scheduled manual pen-testing
RedSpam offers a range of solutions in Penetration Testing.
Ampito offers penetration testing services as part of our broader cybersecurity solutions - RedSpam, helping businesses identify and address vulnerabilities in their systems and networks. We work with partners as well as manual penetration testers.
Automated Testing
Proactive automated testing and scanning on a regular basis for internal and external networks as well as Web Apps and API's.
Human Pen Tests
Human Pen Tests of internal and external networks to provide a point in time assessment to augment an regular scanning solution.
Social Engineering
RedSpam evaluates human security vulnerabilities with social engineering tests like phishing, pinpointing weaknesses and providing detailed reports to strengthen your organisation's defences.
Breach Simulation
Proactively test your defences by safely simulating real-world cyberattacks, to identify and fix vulnerabilities.
How can we help?
Within the RedSpam portfolio, we work with AppCheck and Horizon3.ai, as well as highly regarded Manual Pen Testers. Contact us today for a conversation on how RedSpam can help you leverage the power of Penetration Testing to test and improve your cybersecurity posture.